Spear phishers impersonating Penn Clubs, Office of Student Affairs (OSA), and others attempted to gain access to the accounts of the Penn Post and other student organizations.
Photo Credit: Nicolas Casey
By: Nicolas Casey
Author’s Note: Relevant parties mentioned in this article alongside Penn ISC’s Office of Information Security have been notified in advance of publication. Leadership at Penn Labs—the student organization responsible for the development and maintenance of a number of popular student tools, including Penn Clubs—confirmed with the Penn Post that “[this] is a sophisticated phishing attempt by an unknown third party.”
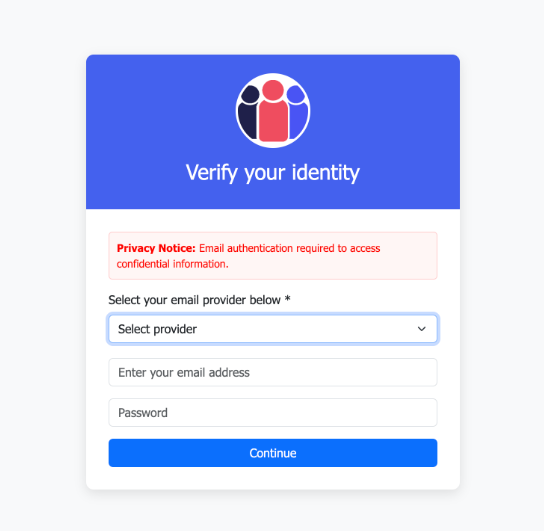
Yesterday afternoon, the Penn Post received an email originating from an account associated with a Catholic grammar school in North Carolina. It claimed that an unspecified “recent database system error” might have caused issues in Penn Clubs’ records, linking to the website pictured below for student club leaders to confirm unspecified email login credentials in an unsecured form.
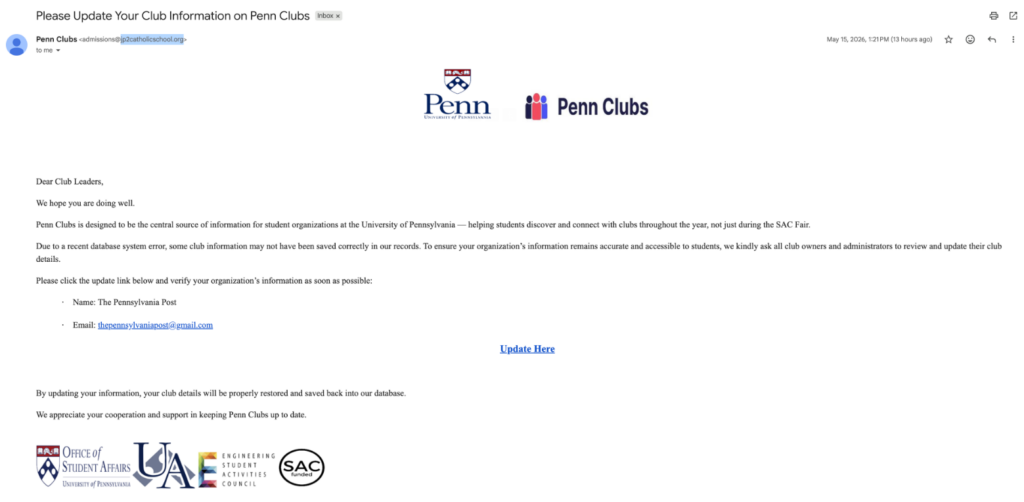
In addition to linking to a domain associated with the Pacific island nation of Vanuatu, the author of the email also claims to be simultaneously representing OSA, the Undergraduate Assembly, Penn ESAC, and the Student Allocations Commission (SAC). This pattern of a reasonably well-drafted email (as far as email scams are concerned, the bar is quite low) claiming to represent specific, trusted entities asking for credential confirmation is a classic example of a form of social engineering-based hacking known as spear phishing.
Within the broader category of phishing, which is any social engineering attack that employs fraudulent messages to manipulate victims, spear phishing is both rare and lethal. A 2023 report by Barracuda Networks, a global cybersecurity company owned by private equity firm KKR, found in an analysis of 50 billion emails that less than 0.1% of them constituted examples of spear phishing. At the same time, they were responsible for 66% of all breeches, in part because of how difficult successful attacks can be to detect if the victim did not realize that they had been phished. Fortunately for Penn’s clubs, Penn Labs identified this attempt well before the industry standard of 43 hours post delivery.
To that end, the Penn Post highly recommends no other student leaders that might have received this—or a similarly fraudulent message—interact with it. If you have accidentally disclosed credentials to this form, contact the Office of Information Security at Penn ISC and follow your email provider’s instructions for securing a compromised account.
Nicolas Casey is a senior in the College studying Mathematical Economics from London, England. He is the Technology Director (Emeritus) for the Pennsylvania Post and can be reached at nickcaseycipres@gmail.com